In this article, we will see you can deploy DNS recursive resolver using Thunder CFW.
Setup
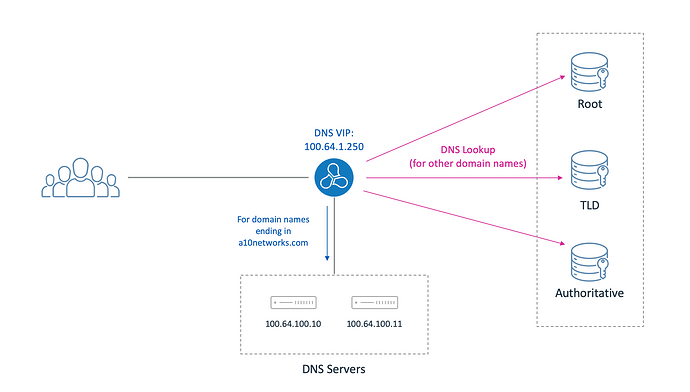
This is what we want to achieve:
By default, the Thunder device should resolve queries starting from the root servers.
- However, for the domain names ending in a10networks.com, it should use the response from a DNS service-group that is bound to the DNS VIP.
Step-by-Step Configuration
Create a NAT pool:
This NAT pool will be used by the Thunder device to send out DNS queries:
ip nat pool IPv4-DNS 100.64.100.250 100.64.100.250 netmask /32
Specify a class list of domain names:
class-list internal-domains dns
dns ends-with a10networks.com
Create a DNS template:
slb template dns dns-enable-template
recursive-dns-resolution
hostnames internal-domains
ipv4-nat-pool IPv4-DNS
default-recursive
Note:
With the “default-recursive” command, the Thunder CFW will by default act as a recursive resolver and try to resolve the DNS queries starting from the root server.
In this case, the domains specified using the class-list specifies an “exception” to this default lookup process – the domains matching the “hostnames ” will be resolved using the service-group that is applied on the VIP (see the next step) instead of the default resolution process (starting from the root server).
Apply the DNS template to a DNS VIP:
slb server RS10 100.64.100.10
port 53 tcp
port 53 udp
!
slb server RS11 100.64.100.11
port 53 tcp
port 53 udp
!
slb service-group SG-DNS-TCP tcp
member RS10 53
member RS11 53
!
slb service-group SG-DNS-UDP udp
member RS10 53
member RS11 53
!
slb template dns dns-enable-template
recursive-dns-resolution
hostnames internal-domains
ipv4-nat-pool IPv4-DNS
default-recursive
!
slb virtual-server DNS-VIP 100.64.1.250
port 53 dns-udp
source-nat auto
service-group SG-DNS-UDP
template dns dns-enable-template
Verification
You can view the statistics for DNS queries resolved recursively using:
vThunder#sh slb virtual-server DNS-VIP 53 dns-udp application-statistics | include Recursive
Recursive Resolution Started: 525
Recursive Resolution Succeeded: 524
Recursive Resolution Send Failed: 1
Recursive Resolution Timed Out: 7
Recursive Resolution Retransmit Sent: 7
Here is a sample packet capture showing the DNS resolution for a website by the Thunder device starting from the root server (in this case, 192.112.36.4):
By doing a packet capture on the DNS servers making up the service group, we can also confirm that the query for the domain name ending in a10networks.com is resolved using the service-group that is bound to the DNS VIP:
Additional Features
You can additionally configure the following features:
· Integrated DDoS protection
· DNS caching
· DNS Application Firewall (DAF)
· Filter DNS queries of type ANY
ip anomaly-drop bad-content 24
ip anomaly-drop drop-all
ip anomaly-drop out-of-sequence 24
ip anomaly-drop zero-window 24
!
icmp-rate-limit 2000
!
slb common
dns-cache-enable
!
slb template dns dns-enable-template
default-policy cache
malformed-query drop
query-type-filter deny
query-type ANY
You can also apply RPZ policy by importing an RPZ file and specifying it under the DNS template.
For this, import the RPZ file as follows:
vThunder(config)#import rpz a10rpz use-mgmt-port scp://a10tme@10.64.4.130/home/a10tme/a10rpz
Password []?
Done.
vThunder(config)#sh rpz
Name DNS template
--------------------------------------------------------------
a10rpz No
Total RPZ number: 1
vThunder(config)#
vThunder(config)#sh rpz debug
Total Class-list Set Error: 0
Total RPZ Parse Error: 0
vThunder(config)#
vThunder(config)#sh rpz a10rpz
Name : a10rpz
DNS template : No
Content:
$TTL 3H
@ IN SOA @ rname.invalid. (
0 ; serial
1D ; refresh
1H ; retry
1W ; expire
3H ) ; minimum
NS @
A 127.0.0.1
AAAA ::1
; PASSTHRU action
www.a10networks.com IN CNAME rpz-passthru.
; NXDOMAIN action
www.netflix.com IN CNAME .
; NODATA action
www.facebook.com IN CNAME *.
32.36.65.13.31.rpz-ip IN CNAME *.
vThunder(config)#
Now apply this RPZ file under the DNS template:
slb template dns dns-enable-template
rpz 1 a10rpz
logging enable
Complete Configuration
Here is the complete configuration for reference:
ip anomaly-drop bad-content 24
ip anomaly-drop drop-all
ip anomaly-drop out-of-sequence 24
ip anomaly-drop zero-window 24
!
ip dns primary 8.8.8.8
!
ip dns secondary 9.9.9.9
!
icmp-rate-limit 2000
!
timezone America/Los_Angeles
!
ntp server time.google.com
prefer
!
interface management
ip address 10.64.4.135 255.255.255.0
ip default-gateway 10.64.4.1
!
interface ethernet 1
enable
ip address 100.64.1.253 255.255.255.0
!
interface ethernet 2
enable
ip address 100.64.100.253 255.255.255.0
!
!
ip route 0.0.0.0 /0 100.64.100.254
!
ip nat pool IPv4-DNS 100.64.100.250 100.64.100.250 netmask /32
!
slb common
dns-cache-enable
!
slb server RS10 100.64.100.10
port 53 tcp
port 53 udp
!
slb server RS11 100.64.100.11
port 53 tcp
port 53 udp
!
slb service-group SG-DNS-TCP tcp
member RS10 53
member RS11 53
!
slb service-group SG-DNS-UDP udp
member RS10 53
member RS11 53
!
slb template dns dns-enable-template
default-policy cache
malformed-query drop
query-type-filter deny
query-type ANY
rpz 1 a10rpz
logging enable
recursive-dns-resolution
hostnames internal-domains
ipv4-nat-pool IPv4-DNS
default-recursive
!
slb virtual-server DNS-VIP 100.64.1.250
port 53 dns-udp
source-nat auto
service-group SG-DNS-UDP
template dns dns-enable-template
!
logging facility local3
!
logging syslog information
!
sflow setting local-collection
!
sflow collector ip 127.0.0.1 6343
!
!
end
!Current config commit point for partition 0 is 0 & config mode is classical-mode
vThunder#